04 May The Evolution of Access: Achieving Continuous Least Privilege Across All Applications
The Problem:
For decades, organizations have relied on provisioning platforms — access request workflows and static role assignments — to manage who gets access to what. The intent is sound: apply least privilege, grant only what’s needed. But the execution degrades over time into permanent entitlements that nobody revokes. A user finishes a project. The role stays. A service account is created for an integration. The credentials never expire. This is standing access — and standing access is standing risk.
The Gap:
Historically, zero standing privilege efforts have focused on high-sensitivity production environments and traditional admin accounts. But modern work is broader than that. Every SaaS tool, every database, every cloud resource carries risk when access is permanent and unreviewed. And it’s not just human identities; Non-Human Identities (NHIs) like service accounts, API keys, and automation pipelines are often the most over-privileged and least governed identities in an organization.
Periodic access reviews and quarterly recertifications can’t keep pace. What’s needed is a shift to Continuous Least Privilege Access — where access is evaluated in real time, not just when someone submits a ticket or an audit cycle fires.
The Solution:
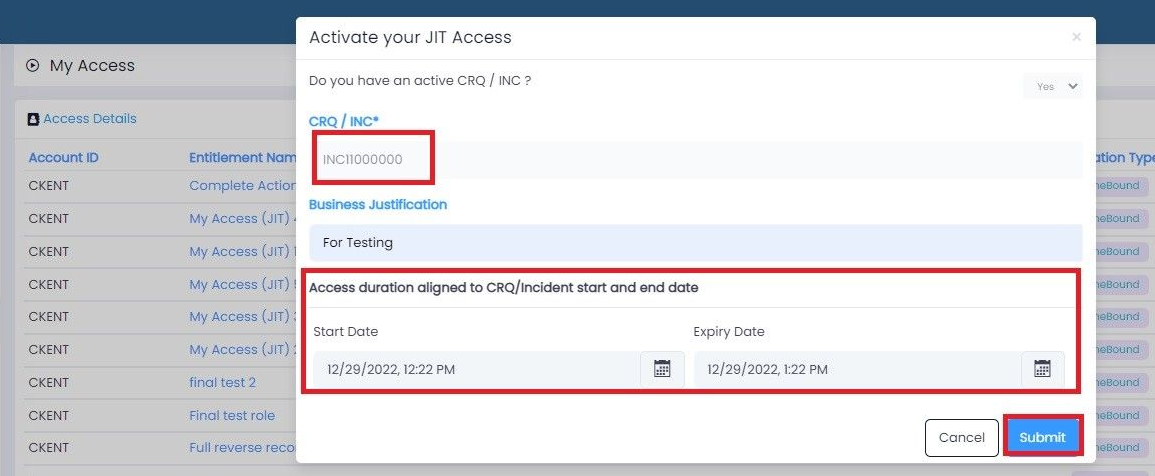
Just-in-Time (JIT) access is the operational bridge
JIT provisioning replaces static, permanent permissions with dynamic, time-bound access that exists only for the duration it is actually needed — and is revoked automatically when the task is complete. No standing privileges. No forgotten entitlements. No blast radius that outlives the work.
- Time-bound by default: Access is granted for the duration of a task and auto-expires — no IT tickets, no manual revocation required.
- Drastically reduced blast radius: A compromised account during a JIT window only exposes what was granted for that session, not everything permanently assigned.
- Automated compliance: Access is inherently tracked and ephemeral, reducing audit burden and eliminating the fatigue of manual review cycles.
- Smart, risk-based approvals: Real-time context enables auto-approval of low-risk requests while routing higher-risk access through appropriate controls.
- Universal coverage, no rip-and-replace: Modern JIT platforms layer on top of existing IAM infrastructure — extending least privilege to cloud, databases, and everyday SaaS without disrupting what’s already in place.
Where to start:
The journey to continuous least privilege doesn’t have to be a big-bang transformation. Start with one or few applications. Identify where standing access is most concentrated — often a privileged admin tool or a shared service account. Enable JIT for that single use case, measure the reduction in standing access, and expand from there. Include NHI identities from day one; they are consistently the most overlooked attack surface.
The standard is no longer static roles and periodic reviews. The standard is continuous least privilege — and JIT is how organizations of any size can get there.
Ready to start your journey:
Confluxsys JIT Provisioning → Explore how lastmile.id delivers JIT access across human and non-human identities, without replacing your existing IAM stack.